Data breaches are an unfortunately common occurrence in the internet age, and it seems like even the tools designed to prevent cybercriminals from accessing your information aren't always up to scratch.
Many cybersecurity experts recommend keeping your passwords completely 'offline' and stored using a pen and paper, and that's part of the reason why companies like Microsoft are moving away from traditional logins in general.
One of the most common forms of advice when it comes to account security is to enable two-factor authentication, which forces you to approve login attempts through an auxiliary source – either an app or email – even with the right details.
Even that might not be as secure as you think, as hackers can still exploit this if they manage to access the details for accounts that approve 2FA requests, and that's why one former hacker has come up with an all-in-one tool to prevent one of the most common causes of data breaches.
Advert

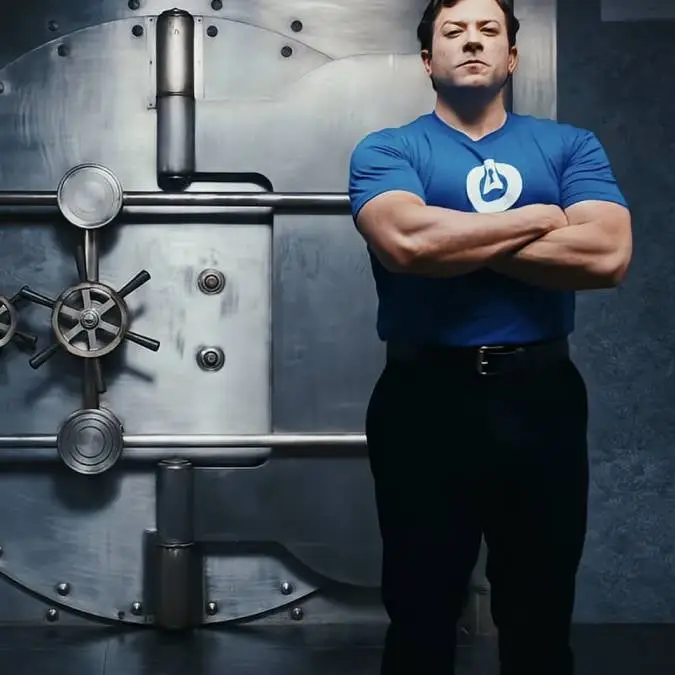
As shared by GB News, ThreatLocker co-founder and CEO Danny Jenkins used to be a hacker himself, but launched his own company to help protect people against the nefarious actions of cybercriminals.
He's always looking for new ways to provide protection against data breaches and phishing attacks, targeting his own employees in elaborate tests to find loopholes and vulnerabilities to work on.
ThreatLocker has now launched an update that aims to transform protection against login breaches, however, claiming that there will be no way for hackers to access your account, even if your data is breached through external means.
"Our transformative solution gives organizations confidence that their systems are secure even if a credential is stolen," Jenkins proclaimed in a talk at the annual Zero Trust World conference.
"Access now requires three things: valid credentials, an approved device, and connection through a secure, ThreatLocker-managed broker. If one step is missing, access is denied, drastically reducing the impact of phishing attacks."

It effectively introduces several fail-safes that need to all be met before you can log in successfully, and while this does lengthen the process overall, it could prove to be vital when it comes to protecting your own personal data and that of the company you work for.
Software like this would have saved certain companies that had their data stolen by hackers through phishing attacks, with ransom figures in the hundreds of millions to return the vital information they needed to proceed as a company.
